⚠️ A config file in .ssh is required to avoid being blocked by potential brute-force attempts ⚠️
Access via SSH JUMPHOST
Access to internal Linux workstations is also available through a Jump Host SSH: jumpsso.fbk.eu using key-based authentication.
JumpSSO allows authentication via Microsoft Entra ID, utilizing SSO and related MFA. Keys are automatically issued after login; these keys are used to pass through Jumpsso (no manual submission to IT is required). Login to the destination machine occurs as follows:
- IT-managed machines in the domain: through user credentials.
- IT-managed machines NOT in the domain: through a public key, which must be requested from [email protected].
- Self-managed machines: through a public key, to be inserted independently.
To access <hostname>.fbk.eu with your default public key, the SSH command is:
ssh -J <nomeUtenteDIDominio>@jumpsso.fbk.eu <nomeUtenteMacchinaDestinazione>@<macchinaDiDestinazione>.fbk.eu
Note: Keys generated by opkssh login are ephemeral and expire after 12 hours. After expiration, you must run the opkssh login command again for new connections (existing open connections will not be closed).
JumpSSO Configuration
Linux/Unix/MAC
- Install the opkssh client (choose one of three ways)
a. download the opkssh client from: https://github.com/openpubkey/opkssh.
b. LINUX:
curl -L https://github.com/openpubkey/opkssh/releases/latest/download/opkssh-linux-amd64 -o opkssh; chmod +x opkssh
c. MAC:
curl -L https://github.com/openpubkey/opkssh/releases/latest/download/opkssh-osx-amd64 -o opkssh; chmod +x opkssh
with CONFIGURAtion file
- Create config file
Run ./opkssh login --create-config, the config file will be created and where it is located. Usually /home/<NomeUtente>/.opk/config.yml
- Edit the config file
Delete all content and paste the following (including ---):
---
default_provider: azureFBK
providers:
- alias: azureFBK
issuer: https://login.microsoftonline.com/11d1b7a3-5e92-4744-83dc-831a43e1f967/v2.0
client_id: 41812210-c0ca-4bb6-b60a-b77fcefe7e55
scopes: openid profile email offline_access
access_type: offline
prompt: consent
redirect_uris:
- http://localhost:3000/login-callback
- http://localhost:10001/login-callback
- http://localhost:11110/login-callback
- Log in to opkssh
Run
opkssh login
This opens a browser for authentication.
Once logged in, an SSH key pair (~/.ssh/id_ecdsa) is created for connecting to jumpsso.fbk.eu.
- Connect via SSH (host jumpsso.fbk.eu)
ssh -J <nomeUtenteDIDominio>@jumpsso.fbk.eu <nomeUtenteMacchinaDestinazione>@<macchinaDiDestinazione>.fbk.eu
common issues
Key Permissions
Change permissions with:
chmod 600 ~/.ssh/id_ecdsa
chmod 644 ~/.ssh/id_ecdsa.pub
- Multiple existing keys and/or Permission denied (ban)
To avoid being accidently banned due to brute force keys, you must create a config file:
COPY THE INFO BELOW to .ssh/config CHANGE THE DATA OF <FBK_login_name> and <host_user>
# Define the jumphost
Host jumpsso jumpsso.fbk.eu
Hostname jumpsso.fbk.eu
User <FBK_login_name>
# Specify a non default private key
IdentityFile ~/.ssh/id_ecdsa
IdentitiesOnly yes
# Match all host except jumphost
Host * !jumpsso
Hostname %h
# Specify a default user name
User <host_user>
# Specify a default private key
IdentityFile ~/.ssh/private_key_file
IdentitiesOnly yes
Windows
Use powershell
WITH CONFIGURATION FILE
To use it you need to:
- Install the opkssh client (choose one of three ways)
a. download the opkssh client: https://github.com/openpubkey/opkssh.
b. winget install openpubkey.opkssh
c. choco install opkssh -y
It is preferable to use a package manager (choco or winget)
- Create the configuration file (IF NOT PRESENT) choosing one of the two ways:
a. Create the folder .opk in C:\Users\<NomeUtente>\ and create config.yml inside the folder
b. New-Item -Path "C:\Users\<NomeUtente>\.opk\config.yml" -ItemType File -Force
- Modify the configuration file (IF NOT PRESENT)
Open the file in C:\Users\<NomeUtente>\.opk\config.yml and copy the following config:
---
default_provider: azureFBK
providers:
- alias: azureFBK
issuer: https://login.microsoftonline.com/11d1b7a3-5e92-4744-83dc-831a43e1f967/v2.0
client_id: 41812210-c0ca-4bb6-b60a-b77fcefe7e55
scopes: openid profile email offline_access
access_type: offline
prompt: consent
redirect_uris:
- http://localhost:3000/login-callback
- http://localhost:10001/login-callback
- http://localhost:11110/login-callback
- Connect to SSH (host jumpsso.fbk.eu )
Run
opkssh login
This opens a browser for authentication. Once logged in, an SSH key pair (~/.ssh/id_ecdsa) is created for connecting to jumpsso.fbk.eu
- Connect via SSH (host jumpsso.fbk.eu )
ssh -J <nomeUtenteDIDominio>@jumpsso.fbk.eu <nomeUtenteMacchinaDestinazione>@<macchinaDiDestinazione>.fbk.eu
common issues
- Key permessions (choose one of the two ways)
The generated key is C:\User\<UserName>\.ssh\id_ecdsa and the permissions must be changed in one of these ways:
a. Right click on the key, Properties, Security, Advanced, Disable inheritance, and remove all users except the one who actually uses the key
b. icacls "C:\Users\<NomeUtente>\.ssh\id_rsa" /inheritance:r /grant:r "<NomeUtente>:F"
- Multiple existing keys and/or Permission denied (ban)
To avoid being accidently banned due to brute force keys, you must create a config file:
COPY THE INFO BELOW in C:\Users\<NomeUtente>\.ssh CHANGING THE DATA OF <FBK_login_name> and <host_user>
# Define the jumphost
Host jumpsso jumpsso.fbk.eu
Hostname jumpsso.fbk.eu
User <FBK_login_name>
# Specify a non default private key
IdentityFile ~/.ssh/id_ecdsa
IdentitiesOnly yes
# Match all host except jumphost
Host * !jumpsso
Hostname %h
# Specify a default user name
User <host_user>
# Specify a default private key
IdentityFile ~/.ssh/private_key_file
IdentitiesOnly yes
Linux/Unix/Mac/Windows10 scp
The syntax of copying via ssh (Secure copy) is:
First of all you need to do opkssh login
scp -o ProxyJump=<FBK_login_name>@jumpsso.fbk.eu local_path <FBK_login_name>@<hostname>.fbk.eu:remote_path
While with a separate public key the command becomes:
First of all you need to do opkssh login
scp -o ProxyCommand="ssh -i ~/.ssh/jump_key -W %h:22 <fbk_login_name>@jumpsso.fbk.eu" - i~/.ssh/jump_key local_path <fbk_login_name>@<hostname>.fbk.eu:remote_path local_path
The simplest is to copy via config_jump configuration file (see point above):
First of all you need to do opkssh login
scp -F config_jump local_path <FBK_login_name>@<hostname>.fbk.eu:remote_path
Note: -o, -F must precede any other option
Linux/Unix/Mac rsync
To use remote sync with the default key, you must add the following to the rsync command:
--rsh "ssh -J <FBK_login_name>@jumpsso.fbk.eu -l <host_user_name>i"
To use remote sync with a different key, you must add the following to the rsync command:
--rsh "ssh -o ProxyCommand='ssh -W %h:22 <fbk_login_name>@jumpsso.fbk.eu'- i ~/.ssh/jump_key -l <host_user_name>"
Remote sync with configuration file requires adding to the rsync command:
--rsh "ssh -F config_jump"
Windows MobaxTerm
On Windows 10/11 we recommend using the built-in openssh client which has a better user experience than MobaxTerm. Again, keys that expire every 12 hours must be imported back into moba after opkssh login.
MobaXterm can use a jump host to connect.
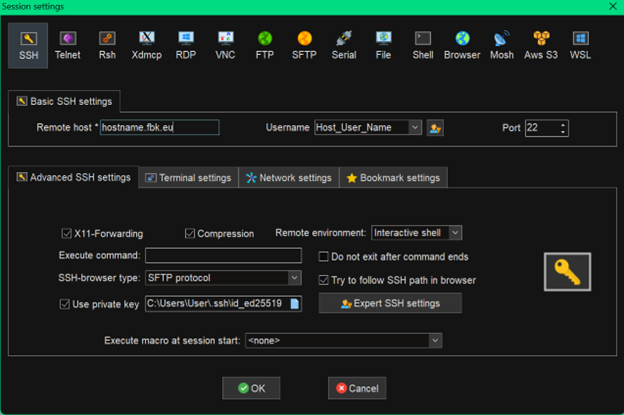
Once a session is created, in Basic SSH Settings you must enter <hostname>.fbk.eu as Remote host, enable Specify Username and add <host_User_name>.
In Advanced SSH Settings enable Use private key and choose the relevant ssh key (openssh format).
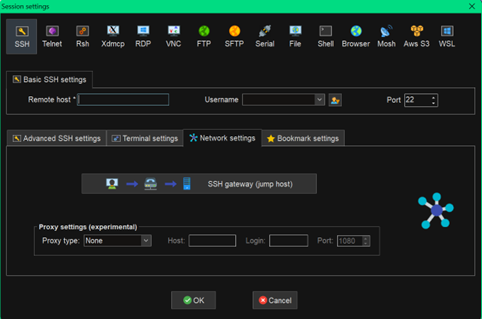
Finally on Network Settings click on the SSH gateway
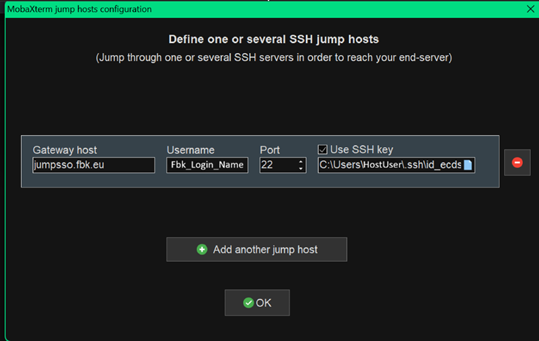
Insert jumpsso.fbk.eu into gateway and specify <fbk_login_name> as User, enable Use private key, and choose its ssh key (the one generated by opkssh login).
Generating SSH keys with MOBAXTERM
For generating and using ssh keys in MobaxTerm see the official documentation: https://mobaxterm.mobatek.net/documentation.html#6_3_2
The generated keys are used to access the target machine and not jump
Windows PuTTY
On Windows 10/11 we recommend using the built-in openssh client which has a better user experience than PuTTY. Opkssh keys expire every 12 hours. So every 12 hours they have to be imported back into putty after opkssh login.
If you still want to use putty you need to install opkssh and setup putty can be done by following this guide: https://github.com/openpubkey/opkssh/blob/main/docs/putty.md
GENERAting SSH keys with PUTTY
For generating and using ssh keys in Putty under Windows: Use SSH Keys With PuTTY On Windows or https://www.ssh.com/ssh/putty/windows/puttygen.
The generated public key is used to access the target machine and NOT jump
Windows WinSCP
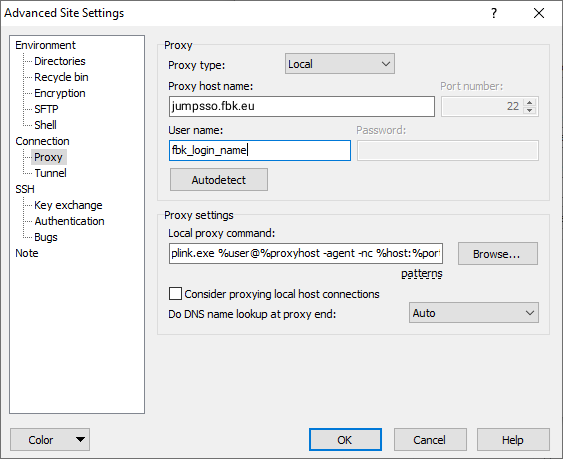
WinSCP can import and use Putty configurations.
Each Putty JumpHost configuration is transformed into a scp configuration when imported via JumpHost with WinSCP.
As with Putty the ssh key must first be inserted into Pageant.
Manual JumpHost configuration can be found in Advanced Site Settings, Connection->Proxy section
Error messages
Common error messages are:
- <login_name>@jumpsso.fbk.eu: Permission denied (publickey).
Re-login on jumpsso with opkssh login - Received disconnect from 217.77.82.20 port 22:2: Too many authentication failures.
All private ssh keys found in $ HOME / .ssh / are sent to the server one at a time. To avoid a key-based attack, after 3 attempts the jump host denies access. Use the IdentitiesOnly and IdentityFile directives (see man ssh config) or the alternative configuration file described above. - Login prompt from internal host
The public ssh key registered for the jump host is not present in the $HOME / .ssh_authorized_keys of the internal server.
For different error messages, send a notification to [email protected]
BASTION
Remote access to internal workstations is available without the aid of a VPN via browser by connecting to bastion.fbk.eu with your FBK credentials.
Supported protocol types are: SSH, VNC, or RDP.
To access the service, send an email to [email protected] with the subject "Add new connection on Bastion" and specifying the following information:
- Protocol type: VNC, SSH or RDP
- Name of the workstation you want to connect to
- Previously user-configured vncserver listening port (VNC connections only)
Once the request has been processed, the connection to the workstation will be made available to the requester: it will then be visible on bastion.fbk.eu
VPN connection request
The FBK trusted network access methods described above cover most of the needs of FBK users.
If you need to use the connection in VPN, from 6/10/25, the new VPN with integrated authentication with Microsoft is available. To obtain it, the user must send an email to [email protected] with the subject "VPN Enabling Request", specifying:
- why you want to use the VPN connection
- if the computer you connect with is self-managed or centrally managed
All information can be found at this link.
DOMANDE E DUBBI FREQUENTI
F.A.Q.
How do I connect to the FBK network from home/university?
To connect to the trusted FBK network, in most cases, you can use BASTION and JUMPHOST. For special needs, send an email to [email protected].